Protect Your Assets with Advanced Edge Security Solutions
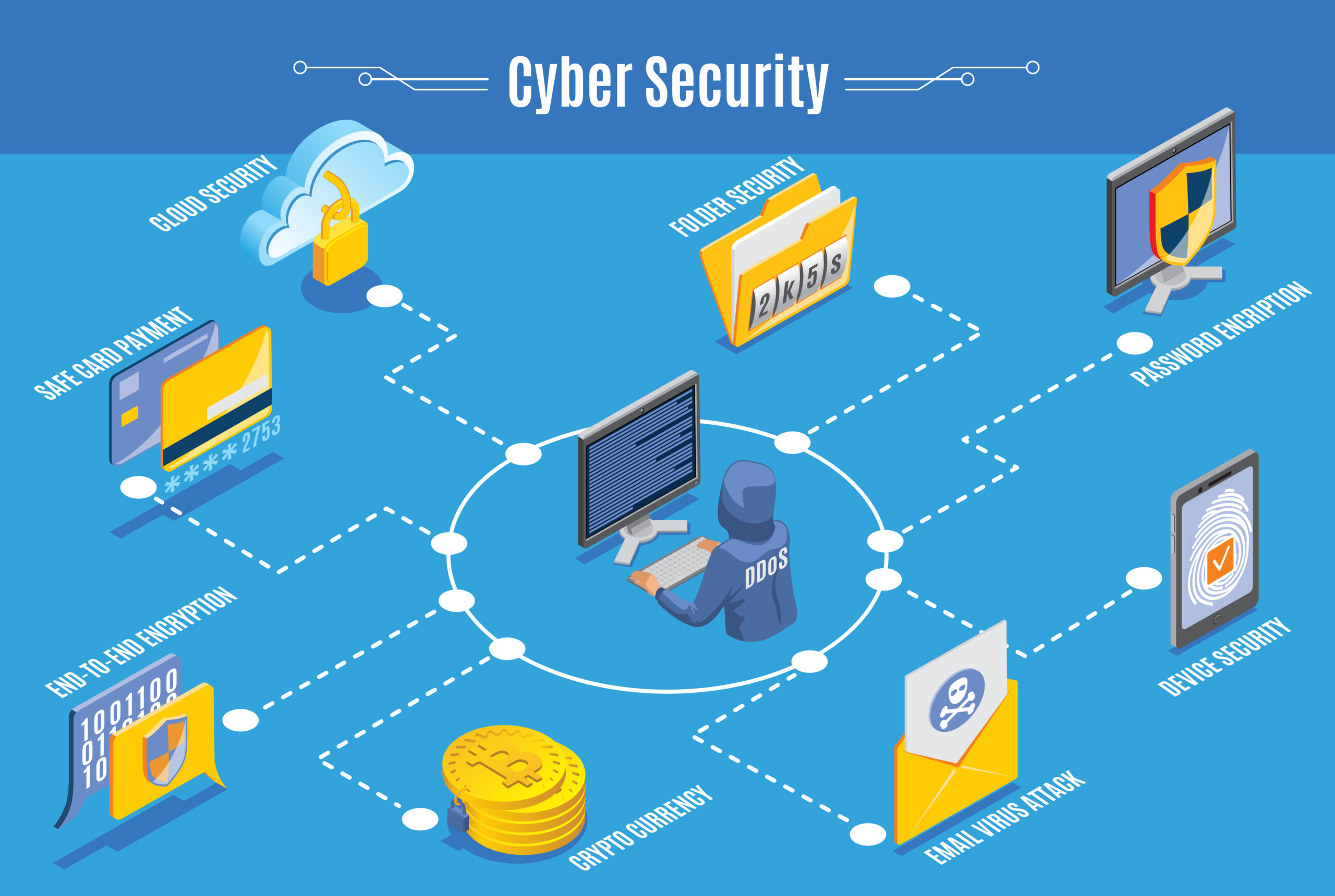
In a digital age defined by connectivity, mobility, and distributed infrastructures, perimeter defense is no longer a simple wall around a centralized fortress. Instead, it is a dynamic and multifaceted strategy critical to protecting modern enterprises. As organizations increasingly embrace edge computing, IoT devices, and cloud-based operations, the traditional perimeter dissolves. This paradigm shift demands […]